TLDR: an awesome cheap device wrapped in Chinese funkiness.
The details
It is hard, very hard to not pay attention to all the funny details that go around the device. But it’s a solid device that performs great for a good price. As far as I can tell, it does not do zooming per se, it is only able to get very close to a subject and thus when the resulting picture is displayed on a bigger screen, small details are visible. As such, what you see is strictly dependent on how close you stick the camera to your subject. In fact the camera has a focus length of a few millimeters to infinity, which means you ca use it a a regular camera but you’ll have to turn the focus knob quite a bit for that.
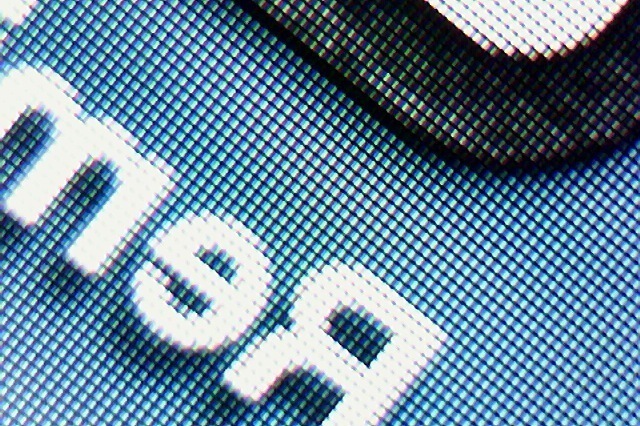
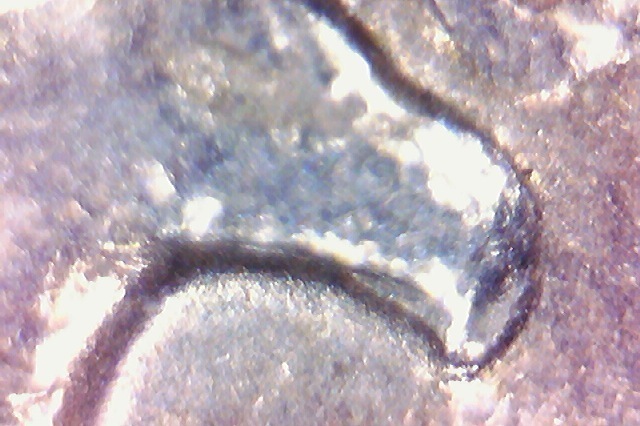
First, some pics of what it’s capable of
They are seriously lacking online
The device itself
On its little tripod
The lens
Everything else
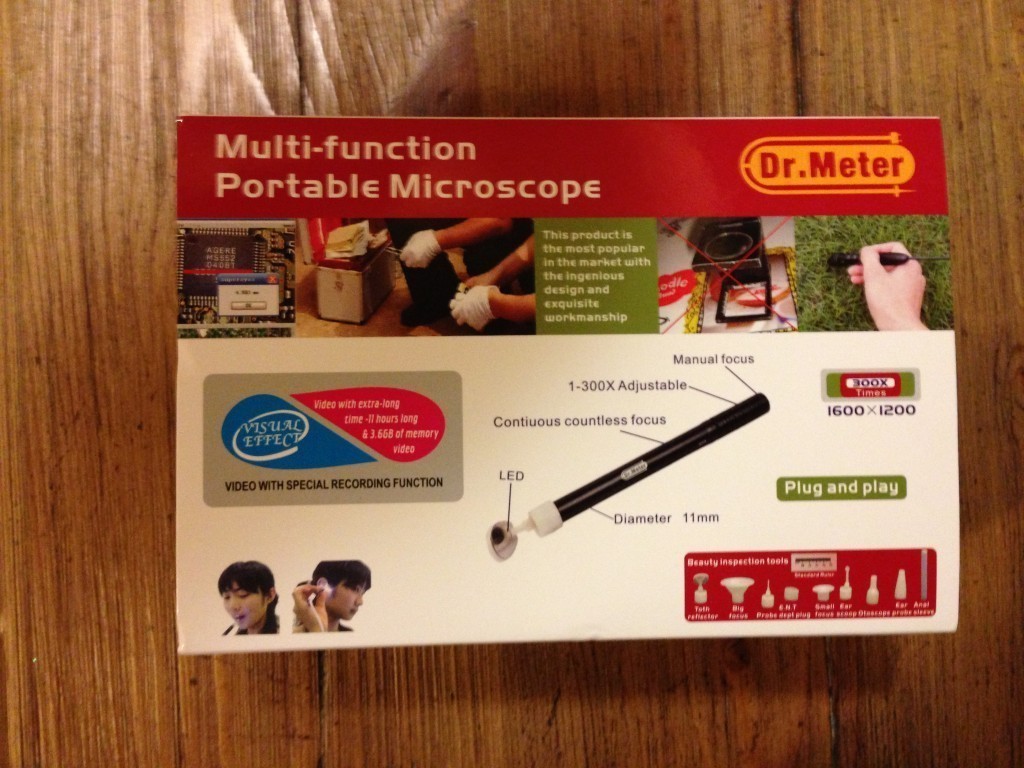
The device has multiple attachments referred to as “beauty inspection tools” which are meant to stick the camera in various orifices of one’s body. They are nicely sealed in sterilized bags (but not the anal one).
Some of the various “beauty inspection tools”…
The unboxing feels like opening a Chinese treasure chest, the mechanism, the texture, the looks; this product is made in China and not pretending otherwise. What else feels Chinese is pretty much anything written in English. It’s super funny to read it all.
Technically
The device is recognized as a standard camera in Windows, MacOS & Linux! No extra drivers necessary. This is what I love about buying products from smaller companies, they go after existing standards. As such you can open it with any webcam software, I took my test shots with photobooth. They provide some software for filming & measuring among other things but I care not about this functionality so I won’t spend the time loading it.
I’ll take it to the beehive this week-end and we’ll see how it does there.